Computer Virus
█ LARRY GILMAN
A computer virus is a program or segment of executable computer code that is designed to reproduce itself in computer memory and, sometimes, to damage data. Viruses are generally short programs; they may either stand-alone or be embedded in larger bodies of code. The
term "virus" is applied to such code by analogy to biological viruses, microorganisms that force larger cells to manufacture new virus particles by inserting copies of their own genetic code into the larger cell's DNA. Because DNA can be viewed as a data-storage mechanism, the parallel between biological and computer viruses is remarkably exact.
Many viruses exploit computer networks to spread from computer to computer to computer, sending themselves either as e-mail messages over the Internet or directly over high-speed data links. Programs that spread copies of themselves over network connections of any kind are termed "worms," to distinguish them from programs that actively copy themselves only within the memory resources of a single computer. Some experts have sought to restrict the term "virus" to self-replicating code structures that embed themselves in larger programs and are executed only when a user runs the host program, and to restrict the term "worm" to stand-alone code that exploits network connections to spread (as opposed to, say, floppy disks or CD ROMs, which might spread a virus). However, virus terminology has shifted over the last decade, as computers that do not communicate over networks have become rare. So many worm/virus hybrids have appeared that any distinction between them is rapidly disappearing. In practice, any software that replicates itself may be termed a "virus," and most viruses are designed to spread themselves over the Internet and are therefore "worms."
A program that appears to perform a legitimate or harmless function, but is in fact designed to propagate a virus is often termed a Trojan Horse, after the hollow, apparently-harmless, giant wooden horse supposedly used by the ancient Greeks to sneak inside the walls of Troy and overthrow that city from within. Another interesting subclass of viruses consists of chain letters that purport to warn the recipient of a frightening computer virus currently attacking the world. The letter urges its recipient to make copies and send them to friends and colleagues. Such hoax letters do not contain executable code, but do exploit computerized communications and legitimate concern over real, executable-code viruses to achieve self-replication, spread fear, and waste time. Chain letters have also been used as carriers for executable viruses, which are attached to the chain letter as a supposedly entertaining or harmless program (e.g., one that will draw a Christmas card on the screen).
The first "wild" computer viruses, that is, viruses not designed as computer-science experiments but spreading through computers in the real world, appeared in the early 1980s and were designed to afflict Apple II personal computers. In 1984, the science fiction book Necromancer , by William Gibson, appeared; this book romanticized the hacking of giant corporate computers by brilliant freelance rebels, and is thought by some experts to have increased interest among young programmers in writing real-world viruses. The first IBM PC computer viruses appeared in 1986, and by 1988 virus infestations on a global scale had become a regular event. An anti-virus infrastructure began to appear at that time, and anti-virus experts have carried on a sort of running battle with virus writers ever since. As anti-virus software increases in sophistication, however, so do viruses, which thrive on loopholes in software of ever-increasing complexity. As recently as January 28, 2003, a virus dubbed "SQL Slammer" (SQL Server 2000, targeted by the virus, is a large software package run by many businesses and governments) made headlines by suspending or drastically slowing Internet service for millions of users worldwide. In the United States alone, some 13,000 automatic teller machines were shut down for most of a day.
All viruses cause some degree of harm by wasting resources, that is, filling a computer's memory or, like SQL Slammer, clogging networks with copies of itself. These effects may cause data to be lost, but some viruses are designed specifically to delete files or issue a physically harmful series of instructions to hard drives. Such viruses are termed destructive . The number of destructive viruses has been rising for over a decade; in 1993 only about 10% of viruses were destructive, but by 2000 this number had risen to 35 percent.
Because even nonmalicious or nondestructive viruses may clog networks, shut down businesses or Web sites, and cause other computational harm (with possible real-world consequences, in some cases), both the private sector and governments are increasingly dedicating resources to the prevention, detection, and defeat of viruses. Twenty to 30 new viruses are identified every day, and over 50,000 viruses have been detected and named since the early 1980s, when computers first became integrated with the world economy in large numbers. Most viruses are written merely as egotistical pranks, but a successful virus can cause serious losses. The ILOVEYOU virus that afflicted computers globally in May, 2000 is a dramatic recent case that illustrates many of the properties of viruses and worms.
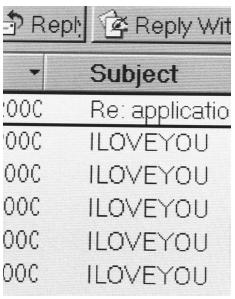
The ILOVEYOU virus was so named because in its most common form (among some 14 variants) it spread by looking up address-book files on each computer it infected and sending an e-mail to all the addresses it found, including a copy of itself as an attachment named LOVE-LETTER-FOR-YOU.TXT.VBS. ("VBS" stands for Visual Basic Script, a type of file readable by World Wide Web browsers.) If a recipient of the e-mail opened the attachment, the ILOVEYOU virus code would run on their computer, raiding the recipient's address book and sending out a fresh wave of e-mails to still other computers.
ILOVEYOU first appeared in Asia on May 4, 2000. Designed to run on PC-type desktop computers, it rapidly spread all over the world, infecting computers belonging to large corporations, media outlets, governments, banks, schools, and other groups. Many organizations were forced to take their networks off line, losing business or suspending services. The United States General Accounting Office later estimated that the losses inflicted by the ILOVEYOU virus may have totaled $10 billion worldwide. Monetary losses occurred because of lost productivity, diversion of staff to virus containment, lost business opportunities, loss of data, and loss of consumer confidence (with subsequent loss of business).
National security may also be threatened by computer viruses and similar software objects. During the ILOVEYOU incident, the U.S. Department of Health and Human Services was disrupted for many hours. An official of the department stated that if a biological out-break had occurred simultaneously with this 'Love Bug' infestation, the health and stability of the nation would have been compromised with the lack of computer network communication. An official at the U.S. Department of Defense stated that so many personnel had to be shifted from their primary responsibilities to deal with ILOVEYOU that if the incident had continued much longer, reservists would have had to be called up. All this damage, and more, was accomplished by a virus not even especially designed to do so. Governments are, therefore, concerned that specially designed viruses and other forms of cyberattack may be used deliberately by hostile governments or terrorist groups to cripple the military or the economy. The U.S. National Security Agency has stated that at least 100 governments are developing viruses and other cyberweapons, as well as terrorist groups. To counter such threats, the U.S. government has established a National Infrastructure Protection Center in the Federal Bureau of Investigation. Its mission is to serve as the central federal point for coordinating information on threats to infrastructure, including threats (such as viruses) to computers and telecommunications networks.
█ FURTHER READING:
BOOKS:
Ferbrache, David. Pathology of Computer Viruses. Germany: Springer-Verlag, 1992.
Fites, Philip, Peter Johnston, and Martin Kratz. The Computer Virus Crisis. New York: Van Nostrand Reinhold 1992.
PERIODICALS:
"Virus Hits A.T.M.s and Computers Across Globe." New York Times. January 28, 2003.
ELECTRONIC:
Brock, Jack L. "'ILOVEYOU' Computer Virus Highlights Need for Improved Alert and Coordination Capabilities." United States General Accounting Office. Testimony before the Subcommittee on Financial Institutions, Committee on Banking, Housing and Urban Affairs, U.S. Senate. May 18, 2000. http://nsi.org/library/virus/ai00181t.pdf (Jan. 28, 2003).
Comment about this article, ask questions, or add new information about this topic: